The Terrifying Truth About the New Mass Surveillance Machine (And What It Means For You)
Advanced analytics, biometrics, and commercial data brokers are being weaponized against citizens. Here is what is happening right now.
For years, privacy advocates and civil libertarians warned that the tools of war developed and deployed overseas would eventually be turned inward. It’s a phenomenon that scholars call “the imperial boomerang.” That day is no longer a theoretical future; it is our current reality. In Minneapolis and elsewhere, we are seeing reports that regime enforcers are using a combination of data from social media, surveillance cameras, commercial data brokers, and even biometrics, together with advanced analytics tools from Palantir, to target Americans.
This is not standard policing. This represents the homecoming—or domestication—of tools and techniques perfected in the U.S. counterinsurgency (COIN) and counterterrorism (CT) campaigns in Iraq and Afghanistan.
Without The Rule of Law, There Is No Law Enforcement
ICE and DHS are not engaged in police work. They are regime paramilitaries, regime enforcers, but not law enforcement. Read more about why that is not a radical take.
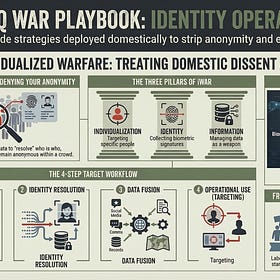
To understand the regime’s strategy, we must understand its tools, techniques, and origins. We are witnessing the use of what the military calls “identity operations,” a key driver of a strategy known as “individualized warfare.”
In this post, the first of a multi-part series, we will focus on the kinds of tools and techniques being deployed by the regime against American citizens. In subsequent posts, we will examine the strategy behind their use, its origins in the “war on terror,” and the potential implications for effective resistance.
The Weaponization of Data & Analytics
While scenes of violent regime actions in the streets of American cities have caught the attention of observers around the world, a battle of data and analytics is being waged largely out of public view. So far, the resistance is losing that battle. But the outcome will shape the degree to which meaningful resistance is possible in the months and years ahead. Let’s review some of the regime’s moves so far.
Social Media & Ad Tech as SIGINT
The regime’s first move in the data and analytics battle is to acquire as much data as possible about each and every one of us. That effort was aided early by the theft and consolidation of vast amounts of Americans’ personal data at the hands of Elon Musk’s so-called “Department of Government Efficiency” (DOGE). But the great DOGE data heist of 2025 was only the beginning.
Regime enforcers increasingly rely on data collected from social media platforms and third party data brokers, all of which provide a form of commercial “signals intelligence” (SIGINT) on us all. For example, DHS has issued administrative subpoenas to Meta (Instagram) to unmask anonymous “community watch” accounts (e.g., @montcowatch) that post the locations of ICE agents. And ICE doesn’t just mask up in the streets. They do so on social media too. A leaked 2026 policy shift allows DHS agents to use alias accounts and “fake identities” to engage with and monitor public online activity and private groups.
Third-party data brokers also help gather data from social media and beyond. ICE has sought contracts with companies like Zignal Labs, which ingests 8 billion social media posts daily, for capabilities like “sentiment analysis” of criticism directed at DHS. In other cases, DHS has sought the integration of utility records, DMV data, and advertising technology data to build comprehensive dossiers.
In December 2025, ICE’s Enforcement and Removal Operations (ERO) awarded a $636,500 contract to a firm named AI Solutions 87 for “skip tracing services nationwide.” The contractor provides “AI agents” intended to accelerate the identification of persons of interest by mapping their entire networks, including service usage, locations, friends, family, and associates.
Then, in January, ICE issued a Request for Information (RFI) to data and ad tech brokers to assess the availability of extensive personal datasets for enforcement purposes. Noting that enforcement actions undertaken without social media information and open-source intelligence often fail, the agency is seeking market research on the acquisition of personal, financial, health, and location data.
Phones, Faces & Fingerprints
Regime enforcers also collect data on Americans through physical encounters with them. This includes the collection of device data at protests or during arrests. For example, ICE employs several phone‑tracking tools, including L3Harris “Stingray” cell‑site simulators that mimic cell towers to locate nearby devices. They also use commercial location‑data subscriptions, such as Penlink’s Webloc, which let agents geofence areas and monitor all phones within them. For digital forensics, ICE contracts with firms like Paragon Solutions for remote spyware, Cellebrite for extracting data from seized but locked phones, and Finaldata’s FINALMobile for recovering deleted files, all of which require physical possession of the device.
Paragon Solutions is an Israeli firm that produces remote spyware capable of hacking phones. While its purchase by ICE was briefly halted by the Biden administration in 2024 over concerns that foreign‑linked spyware could threaten U.S. security, the freeze was lifted by the Trump regime in 2025. Cellebrite has been the subject of controversy in the past for having sold its products to repressive regimes that used it to target journalists and activists, though the company later rescinded those contracts.
But a physical encounter with regime enforcers opens activists to more than just the collection of cell phone data. Being arrested or merely detained can subject one to the collection of various kinds of biometric data, including fingerprints, photos of one’s face, and even collection of one’s DNA. Recently, DHS has transitioned from static, centralized biometric records to a dynamic, field-level surveillance stack designed for real-time identification of domestic targets.
Central to this evolution is Mobile Fortify, a field-deployable application, enabling agents to perform instantaneous facial recognition and fingerprint matching—a capability that has already been documented scanning the faces of legal observers and protesters in Minneapolis and Chicago without consent.
This tactical edge is further sharpened by a $9.2 million contract with Clearview AI, which grants ICE access to a database of 50 billion images scraped from the public internet, explicitly to identify individuals associated with “assaults against law enforcement“—a label civil rights groups warn is being weaponized against non-violent protesters.
To close remaining identification gaps, the agency has invested $4.6 million in BI2 Technologies’ iris-scanning smartphones and proposed a sweeping rule to mandate the collection of palm prints, voice recognition, and DNA from a broader range of individuals, including U.S. citizens and children.
This integrated biometric regime effectively transforms the American public square into a persistent screening environment where records from an increasingly integrated collection of government and private databases are cross-referenced in seconds to catalog and track domestic dissent.
The All-Seeing Eye of Fusion & Analytics
Data from DOGE, data brokers, social media, cell phones, and biometrics--it all adds up fast. Without the ability to sort through it all quickly and effectively, it’s just digital noise. That’s where the regime’s core analytical infrastructure comes in.
Palantir serves as the backbone of the regime’s ability to “fuse,” analyze, and weaponize all of this data. The software, used by military and intelligence agencies during the “war on terror,” ingests massive amounts of data, allowing analysts to sort it into various visual forms, including interactive geospatial maps, social network graphs, timelines, histograms, and more.
Journalists have only begun to document the various ways that this tool is being used. For example, investigators have documented the creation of what was called “ImmigrationOS.” This was a $30 million contract for a platform designed for “near real-time visibility” and “granular tracking” of individuals throughout the immigration and enforcement lifecycle.
Other Palantir tools include ELITE (Enhanced Lead Identification & Targeting for Enforcement) and AFI (Analytical Framework for Intelligence). The first provides a map-based interface described by agents as “Google Maps for raids.” It uses generative AI to extract data from warrants and provides “address confidence scores” to guide enforcement. The second is used for link analysis and geospatial mapping, integrating government records with commercially sourced data to identify “security risks.”
Conclusion
In this first part of the series, we have reviewed the advanced data aggregation tools—from social media monitoring to mobile forensics and biometrics—that are now actively deployed against Americans by the Trump regime. This represents a significant shift from traditional policing toward an aggressive, data-driven approach to repressing all forms of dissent. The scale of data collection, fusion, and analysis, largely powered by platforms like Palantir, is rapidly eroding the possibility of anonymous resistance to the ever-growing tyranny in America.
While I have detailed how the regime is gathering data and building dossiers, the next installment in this series will expose the underlying strategy of “individualized warfare” that these technologies are designed to implement. I will trace its origins directly back to U.S. counterinsurgency (COIN) and counterterrorism (CT) operations in Iraq and Afghanistan. The very intelligence and analysis infrastructure created to “find, fix, and finish” so-called “high-value targets” in far-off warzones is being rapidly deployed against American citizens.
Second Post in the Series 👇
The Military Strategy You've Never Heard Of Being Used To Crush Dissent
In Minnesota and elsewhere, we have seen the rapid expansion of regime mass surveillance directed at American citizens engaged in First Amendment-protected activities. In my last post, the first in this series, I detailed the tools and techniques being deployed. These include the collection of personal data from social media platforms and third party da…
Resistance School Short Courses
I am planning to offer a series of short courses focused on digital security and open source intelligence topics that will be of benefit to those of us engaged in resistance activities. Here are the three I ideas I have to start:
Encrypted Organizing: Secure Communications & Data in an Age of Mass Surveillance
Dox Defense 101: Clean Up Your Online Footprint to Defend Against Doxxing & Online Harassment
Person Of Interest Research: Investigate the Online Footprint of Digital Bad Actors
Do you have other suggestions? Please drop them in the comments. I’m looking to create a regular series of 60-90 minute courses on actionable topics.





Love the idea of Resistance courses!
Great work. Love the resistance courses. Happy to help if you ever need any logistical or other support!