The Regime’s Military Playbook For The Next Phase Of Its War on Dissent
From mass surveillance to physical targeting, here is what the military's "individualized warfare" playbook says is coming for American activists.
Over the last few weeks, we have watched the Trump regime deploy a staggering array of military-grade mass surveillance tools against American citizens, specifically targeting those engaged in First Amendment-protected activities in Minnesota and across the country. As I detailed in the first part of this series, regime enforcers (e.g. ICE, CBP, etc.) are not just passively monitoring the streets. They are utilizing cell phone forensics, biometric scanning, and the advanced data fusion capabilities of Palantir to build comprehensive, actionable dossiers on individual pro-democracy activists.
This is not standard domestic policing; it is not legitimate “law enforcement.” As we established in part two of this series, this is the literal, domestic application of military-style “identity operations.” The regime is ripping pages directly from the U.S. military’s counterinsurgency playbook used in Iraq and Afghanistan. By treating American citizens as “insurgents” and “terrorists,” they are actively working to strip away your anonymity and positively identify every individual within the resistance.
But mass surveillance and identification are never the end goals of this military doctrine; they are merely the prerequisites for what comes next: individualized, even personalized targeting. To survive the escalation, we must understand exactly how this military playbook executes targeting—both in the informational and physical domains—so we can strategically prepare our defenses. In this post, we will start with the physical domain.
A note on sourcing: As with the last post, I will rely mostly on Glenn Voelz’s 2015 book [PDF] on individualized warfare as it is the most comprehensive treatment. All information comes from that source unless otherwise noted.
Please consider becoming a paid or free subscriber to help support my work.
Find. Fix. Finish.
I’m going to cut right to the chase here. While identity operations and individualized warfare may have been inspired at least in part by the confluence of big data analytics and algorithmic targeting in the private sector, the primary military use of these methods during the “war on terror” was physical rather than informational.
Identity operations were the enablers of the kill/capture missions against individual “high-value targets” in Iraq and Afghanistan. These were usually key leaders, bomb makers, propagandists, or anyone else deemed to be a “key node” in the adversary “network.” When you heard on the news about a high-ranking leader being killed in a drone strike or special forces raid, that was individualized warfare in action and it was enabled by identity operations.
The central idea was to map the enemy network and then capture or eliminate its key human “nodes.” To execute these operations against high-value targets, the military relied heavily on Social Network Analysis (SNA). At the tactical level, SNA was used to conduct exhaustive “pattern of life” analyses. This involved documenting the associations and activities of individuals and groups, culminating in detailed “target information folders” for specific individuals. These dossiers aimed to track every facet of an individual’s existence, including physical descriptions, association, habits, movements, financial transactions, cell phone numbers, and biometric data (sometimes even including DNA samples).
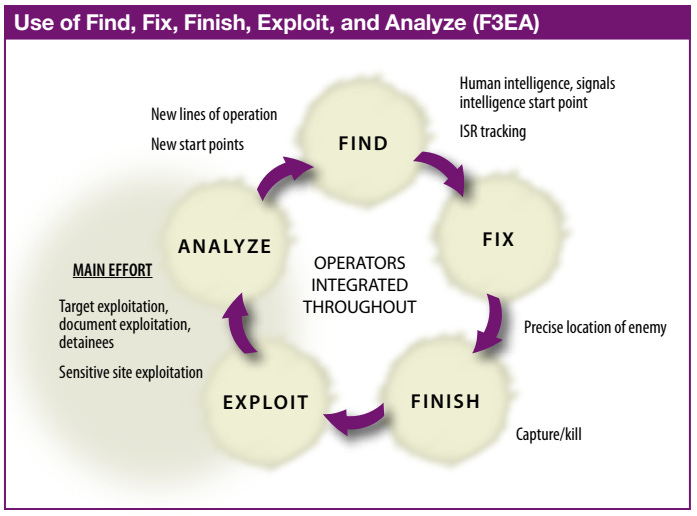
This targeted approach was formalized into military doctrine through frameworks like “Attack the Network” (AtN) [PDF] and the “F3EAD” targeting cycle. F3EAD—which stands for Find, Fix, Finish, Exploit, Analyze, and Disseminate—was explicitly developed as a systematic approach to personality-based targeting. The method’s creation is often credited to disgraced former Lt. Gen. Michael Flynn, who was forced to resign as National Security Advisor during Trump’s first term after he misled the White House about his conversations with Russian officials. Flynn later played an important role in promoting the January 6 insurrection.
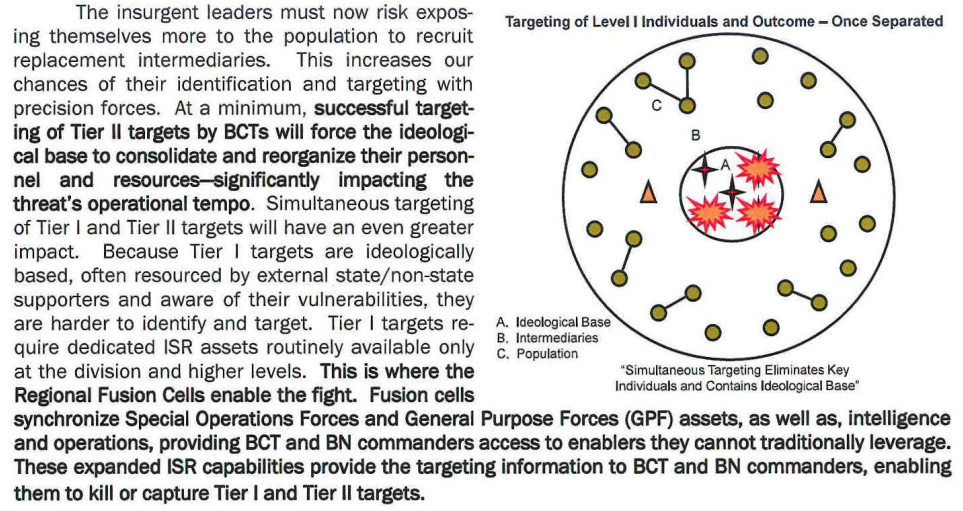
Operating within the broader AtN framework, F3EAD functions by sub-categorizing individuals into categories by priority. So-called “tier-one targets” include top-level leadership figures. “Tier-two targets” are intermediaries and facilitators who link leaders to the rest of the organization and to the general population. Finally, “tier-three targets” are low-skilled foot soldiers and general threats among the public.
Source: Flynn, Michael T., Rich Juergens, and Thomas L. Cantrell. “Employing ISR SOF Best Practices.” Joint Force Quarterly, no. 50 (3rd Quarter 2008): 57–63. https://apps.dtic.mil/sti/tr/pdf/ADA516799.pdf. [Accessed 19 March 2026].
The strategic goal of applying this intense network analysis to a population is to systematically neutralize the larger organizational structure by removing highly connected tier-one and tier-two targets. The idea is that if the most highly connected “nodes” in the network are eliminated, the network will suffer catastrophic, cascading failures. It’s the same idea behind the expanding series of leadership “decapitation strikes” in Iran right now.
Source: “Attack The Network Part 1: ‘ Oil Spot Methodology,” Asymmetric Warfare Group (March 2009), https://nllp.jallc.nato.int/cmnt/ciedcoi/Library/Attack%20the%20Network%20Methodology%20Part%20I.pdf [Accessed 19 March 2026].
During the 2007 military “surge” in Iraq, military “fusion cells” utilized identity operations techniques to locate, target, and then kill or capture key individuals within insurgent cells and militias. John Nagl, one of the primary architects of this counterinsurgency doctrine, observed that the adoption of Social Network Analysis forced a fundamental shift in how the military operated, moving
“the Army’s intelligence system away from a focus on analysis of conventional enemy units toward a personality-based understanding of the networks of super-empowered individuals.” [Quoted in Voelz 2015]
To process the enormous amounts of data required to map these human networks on the battlefield, the Department of Defense deployed advanced analytical tools like Palantir. As we have already established, the regime is now actively weaponizing these exact same platforms domestically. They are very likely mapping our associations and classifying organizers as tier-one and tier-two targets.
While individual activists are not yet being targeted for physical capture or elimination, the identity operations necessary to enable such actions are well underway.
Drones, DNA & Neuroweapons
If all of this sounds terrifying, that’s because it is. But the future that some military theorists see for identity operations-fueled warfare is even more frightening. In this future, targeting is not merely individualized--i.e. focused on single individuals to eliminate, capture, or influence--but also personalized. Not only will individuals be targeted, but they will be targeted in ways tailored to their unique biology or psychology. Worse yet, the capabilities needed to engage in this kind of warfare are no longer limited to the government.
The integration of facial recognition software with autonomous drone swarms will soon allow authoritarians to automate targeted physical violence on a mass scale. Defense experts predict that in the near future, militaries will be able to launch swarms of drones programmed to roam battlefields and hunt for very specific individuals [PDF]. When we consider that the Trump regime is already utilizing commercial data brokers and advanced analytics to build biometric dossiers on pro-democracy activists, the leap from digital tracking to autonomous physical targeting is perilously small.
Advances in bioscience are paving the way for hyper-personalized biological and neurological weapons designed to disable or kill specific individuals. Military theorists have outlined the potential for DNA-linked bioweapons—viruses engineered to attack a single person based on their unique genetic code. Others have theorized about the potential uses for so-called “neuroweapons.” (See chapters 11, 12 & 14 in PDF.) Neuroweapons are targeted drugs, toxins, or microbes that could be deployed to alter brain function, triggering neuro-psychiatric disorders or selectively manipulating the cognition and behavior of key resistance leaders. The regime’s goal in utilizing such tools would not simply be death, but the psychophysical disruption and neutralization of the resistance’s most vital human “nodes.”
While individualized warfare was once the exclusive domain of wealthy, technologically advanced states, off-the-shelf drone and facial recognition technologies are already accessible to the general public. As the regime continues to radicalize its base and unleash domestic paramilitaries, we must prepare for the reality that extremists and regime-aligned vigilantes could also soon possess the tools to conduct their own localized, identity-based targeting operations.
“Writing in the seventeenth century, Thomas Hobbes famously asserted that humanity’s original ‘state of nature’ must have been a ‘warre of all against all’. The growing individualization of warfare suggests that this may be our all too real future, as well as our imagined past.”
- Rosa Brooks, How Everything Became War and the Military Became Everything
Conclusion
Over the course of the last three posts, we have seen how the mass surveillance regime is spreading and being used against the pro-democracy resistance across the country. We’ve also seen that the tools and techniques used by the regime have their roots in “war on terror” concepts of “identity operations” and “individualized warfare.” In this post, we looked at exactly what the application of those concepts meant on overseas battlefields and what military theorists think they will look like in the future.
We have not yet seen the worst of what individualized warfare can deliver. More likely, before they turn to physical attack as described above, the regime will attempt to neutralize our human “nodes” through highly targeted psychological and information operations. In the next installment of this series, we will examine the informational domain of individualized warfare, detailing how the military playbook uses tailored deception and manipulation to divide and conquer from within.
The material covered thus far in this series is frightening. My goal is not to frighten or offer more doom and gloom. The goal is to inform and educate. To do so, we must face the horrible reality of our situation.
Understanding these tactics is our primary line of defense, and in a subsequent post, we will dive more deeply into the specific operational security (OPSEC) and strategic resistance measures required to survive and defeat these threats. Do not give in to despair; history proves that armed with knowledge and unyielding solidarity, we possess the ability to outlast their chaos and win.
The regime’s adoption of military counterinsurgency tactics against American citizens is fundamentally a sign of profound weakness. As students of resistance, we know that a regime relying on such tools is not a legitimate government. It is a desperate occupation force terrified of its own people. They want you paralyzed by the science-fiction horror of these weapons. But a regime that must hunt its citizens individually is a regime that has completely lost the consent of the governed. Dictatorships always project an illusion of omnipotence right up until the moment they collapse under the weight of organized, strategic noncooperation.
I am an academic researcher and independent analyst working to inspire and educate the resistance with evidence-based analysis. Please consider becoming a paid or free subscriber to help support my work.






The threat architecture described here is real and documented. I've traced the Palantir lineage from Total Information Awareness (killed by Congress in 2003) through venture capital resurrection to ImmigrationOS — the system ICE uses today. BI Incorporated runs the invisible layer: private investigators, commercial databases, ankle monitors, facial recognition.
But here's what Minneapolis proved: distributed witness networks can outpace centralized surveillance. The infrastructure that defeated 3,000 federal agents in 22 days wasn't a counter-surveillance operation. It was 80+ organizations coordinating through Signal, dispatching observers within minutes, maintaining six camera angles on every encounter.
Surveillance serves whoever controls the apparatus. Witness serves the shared orientation.
The alarm is correct. The response is organization — not matching their technology, but building the human infrastructure they can't map, can't predict, and can't outpace.
Bureaucracies repeat. Networks adapt.
The full framework: https://theramm.substack.com/p/the-moral-battlefield
The surveillance architecture: https://theramm.substack.com/p/the-closed-loop
How the network spreads: https://theramm.substack.com/p/the-moral-battlefield-part-3-the
I believe this regime is evil enough to plan to do this to us. But, as horrifying as it sounds they have gravely underestimated the super majority of American’s profound patriotism and love for our democratic republic. Ironically, I believe this would be the ONE thing that would actually unite MAGA, liberals and all of our children, grandchildren, nieces, nephews, cousins, parents, etc who honorably serve in our military to protect OUR families and OUR Constitution - those who serve and are actually trained to fly drones, fly our bombers and fire our ammo. I’m confident you couldn’t find a veteran or current military member in the Trump, Miller, Thiel, Vance, Vought, etc families, that will fight to protect them if they attack us on our soil.