How the Regime Will Weaponize Our “Digital Dust” (And How To Prepare)
From targeted psychological operations to digital deception, here is the playbook for regime information warfare against American citizens.
Over the last three posts, we established that the Trump regime is building a mass surveillance infrastructure to map and disrupt the resistance. In the worst case scenario, that infrastructure will allow the regime to execute the physical targeting phase of individualized warfare. This would involve the kinds of kill/capture missions carried out with drone strikes and special operations raids against so-called “high-value individuals” and “key nodes” in Iraq and Afghanistan.
If you have not done so already, please do read the previous posts so that you understand that the tools to allow such a future are very real and are migrating to domestic operations against pro-democracy activists right now.
The Terrifying Truth About the New Mass Surveillance Machine (And What It Means For You)
The Military Strategy You’ve Never Heard Of Being Used To Crush Dissent
The Regime’s Military Playbook For The Next Phase Of Its War on Dissent
But before the regime escalates to this kind of physical force, they will attempt to neutralize the most high-value “human nodes” in the resistance network on the digital battlefield. As Glenn Voelz notes in his book on individualized warfare [PDF], cyberspace has become the premier battleground for “phase zero” operations, which are “designed to shape perceptions and influence behavior as a precursor to kinetic action.” By leveraging the data they have collected on us, the regime is very likely to wage a personalized informational and psychological war on us in an effort to prepare the “battlefield” for what comes next.
Hyper-Personalized Information Warfare
To understand how this informational targeting works, we must look at how the U.S. military has historically used psychological operations (PSYOP) against adversaries. Psychological operations are nothing new, of course. The idea of deceiving or otherwise shaping an adversary’s perceptions and beliefs as a way of undermining their will to resist is as old as warfare itself. Like other forms of warfare, though, developments in information and communication technologies, especially the rise of the internet and social media, have enabled more precision targeting of messages and information.
Voelz points to the CIA’s Phoenix Program in Vietnam as an early precursor to the hyper-personalization of information warfare. More recently, the 2003 invasion of Iraq saw U.S. forces sending “thousands of personal e-mails” directly to Iraqi military officers urging them to abandon their posts.
The Middle East is not the only region where the United States has honed these capabilities in recent decades. The U.S. military successfully dismantled Joseph Kony’s Lord’s Resistance Army (LRA) through “precision PSYOP targeting.” By utilizing intelligence from family members and mapping social networks, Special Forces were able to “identify key leaders within the LRA that were prone to defection” and target them with tailored messages via radio, leaflets, and aerial loudspeakers. Message by message, the military systematically dissolved the group from within.
Of course, the United States is not the only nation to use such tactics. Russia has demonstrated how these targeted informational tactics can be weaponized against a modern, digitally connected population in Ukraine. Rather than relying solely on broad propaganda, Russian forces and their proxies launched “targeted information operations” directly at Ukrainian soldiers and their families. Utilizing social media intelligence (SOCMINT), Russia sent highly personalized, threatening text messages to Ukrainian soldiers on the front lines, such as, “You are encircled. Surrender. This is your last chance.” The direct impact of these tailored operations was the “demoralization and significant consternation” of the Ukrainian forces, deliberately stressing the trust between soldiers and their command structures [PDF].
The Ukrainians have countered with individualized information warfare operations of their own. In one case, early in the war, Ukraine made captured Russian soldiers call their mothers. The calls were video recorded and then broadcast for the world to see. Videos of the calls went viral on social media. Ukraine also weaponized mass doxxing when a newspaper leaked the personal information of some 120,000 Russian soldiers.
In other cases, international supporters of Ukraine also got in on the action. A Norwegian computer expert and a team of global volunteers targeted ordinary Russian civilians with mass email campaigns, sending over 22 million messages urging them to seek out independent information about Russia’s invasion of Ukraine and reject the war. Polish hacktivists undertook a similar campaign. In that case, they weaponized a collection of 20 million Russian phone numbers and 140 million email addresses by creating a website that would let anyone send text messages or emails to the owners of those numbers and addresses.
The Future of Individualized Psychological Warfare
The most immediate danger to the American resistance is that our increasingly connected lives provide the regime with the exact ammunition needed to execute these kinds of hyper-personalized information operations against American pro-democracy activists. We are currently undergoing what Voelz calls an “identity merger,” where our physical documents, behavioral patterns, and social media habits create a persistent, multidimensional composite of who we are. Voelz says that this “composite” identity is
“defined by deeply embedded relationships derived from analytical correlations rather than explicit information. These implicit identities will not be defined by format and will blur the existing distinctions between biographic, biometric, behavioral, and digital information. These composite identities will be persistent, cumulative, and associative--meaning that they will be based on information that endures forever in digital archives, is constantly accumulating as new data points, and contextually enriched through deep correlation to other people, places, and activities. These new identities will not exist as discrete nodes of data, but rather will be defined in the context of their relationship to other things. Thus, this future identity concept will be one that is inherently networked, temporally deep, and multidimensional in ways that current identities are not.
[...]
“One implication of this identity merger will be the potential for more powerful means of passive monitoring and surveillance. [...] Under Secretary of Defense for Intelligence Mike Vickers recently observed how the tracking of individuals around the globe has become easier in recent years due to ‘the digital dust that we all leave around [as] we lead our lives.’”
Voelz was writing over a decade ago now. This was the era of Cambridge Analytica, when ill-begotten Facebook data was used to psychologically profile users and then micro-target them with manipulative political advertising. Since then, the tools and techniques of data analytics and targeting have only improved while we have all contributed an extra decade’s worth of personal information to the digital dustbin of big data. One can look to China’s GoLaxy campaign for how generative AI is already being incorporated into targeted information warfare campaigns and where the future might take us.
As with the physical domain, the future that theorists see for the cognitive domain is equally dystopian and includes some of the same technologies, including the terrifying intersection of biological disruption and targeted digital disinformation. Defense planners are actively theorizing the use of those neuroweapons we saw in the last post, but this time as weapons of mass disruption, where the use of neurotropic agents could be paired with the intentional “Internet messaging of narratives” designed to amplify panic, overwhelm public health systems, and foster the rapid “dissolution of public trust” [PDF].
So-called “neuro-cognitive intelligence” or “NEURINT” has also been discussed as a way to alter individual and group thought as a means of optimizing future psychological operations [PDF].
Conclusion
In summary, the application of identity operations in the informational and psychological domains would represent a systematic effort to weaponize our personal data against us. From the tailored emails sent to Iraqi officers to the precision psychological operations that dismantled the Lord’s Resistance Army, the strategy has always been to identify and neutralize key “human nodes.”
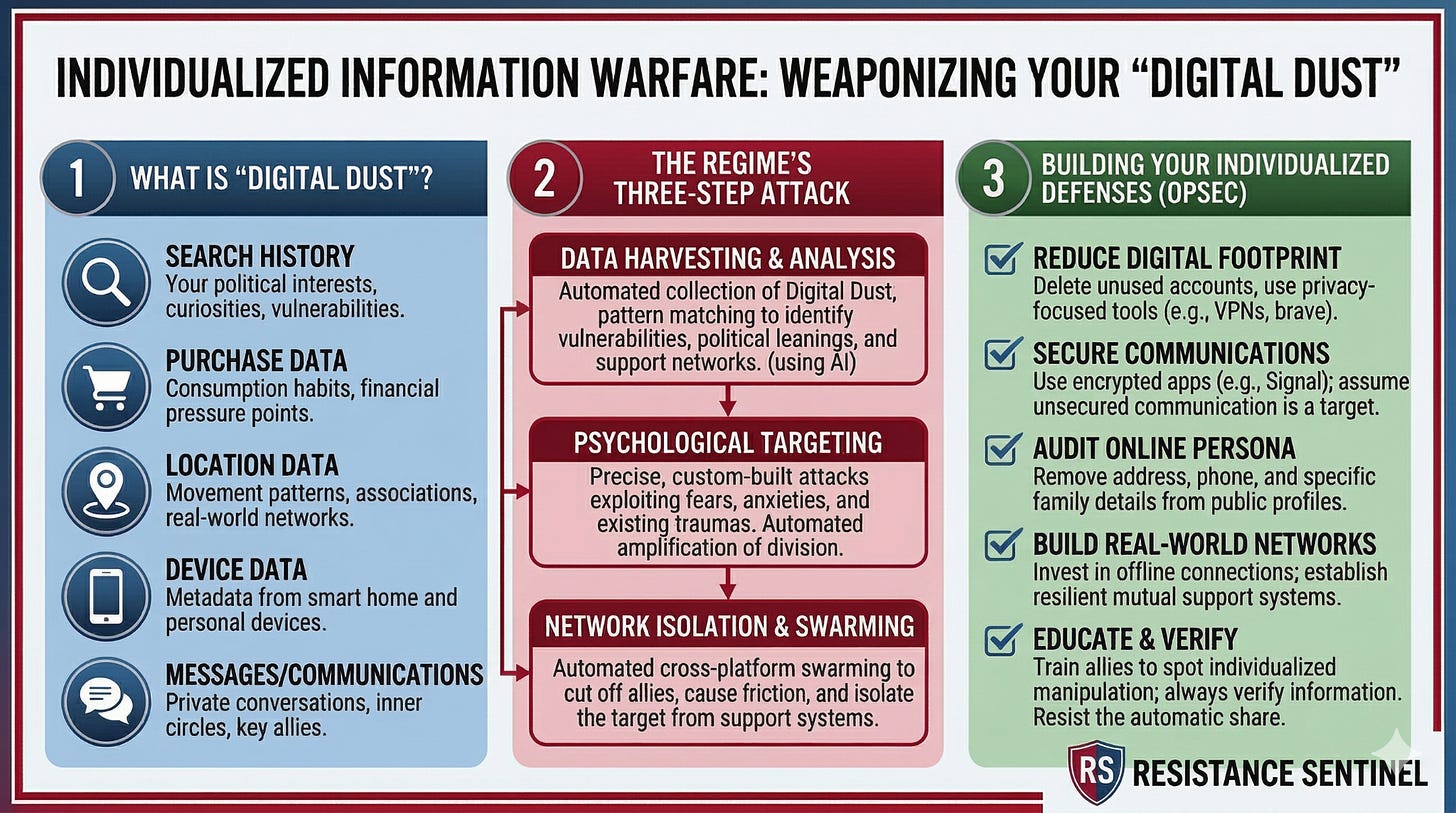
Today, our interconnected lives provide the regime with the exact “digital dust” needed to execute these operations domestically, allowing them to map our networks and target us with personalized disinformation. As defense experts have warned, the ultimate evolution of this warfare combines physical disruption with targeted online narratives designed to completely dissolve public trust and the ability to dissent.
This hyper-personalized approach to crushing dissent is intended to make you feel isolated, terrified, and powerless. But understanding the playbook is the first step to defeating it. As students of resistance, we must recognize that this reliance on psychological manipulation and digital trickery is a symptom of authoritarian fragility. A regime that has the true consent of the governed does not need to wage individualized physical or psychological warfare against its own citizens.
So how do we begin to prepare?
Recognize What is Happening: By reading this series, you now know the capabilities and playbook for individualized warfare. You know they are being deployed. But you also know that the worst case scenarios are not here yet. We still have time.
Expect Digital Deception: We must assume that the regime will use our digital footprints against us to divide our coalition and break our morale.
Secure Your Networks: We must practice strict OPSEC to deny the regime the social network maps they need to target us. I have already written some about this HERE and HERE. I have future posts planned, as well as short video courses, that will provide more detailed steps that we can take.
Maintain Solidarity: The goal of informational warfare is to divide and conquer. We counter it by maintaining trust in one another and refusing to let targeted fear break us. Give others grace. Lift each other up. But always be on the lookout for those within the resistance who would turn us against one another over petty grievances or disagreements. When you see others engaging in that way, encourage them to reconsider their tactics. If they persist, ignore and isolate them, and then move on.